Tag: SIEM
-
Analyzing & Detecting IIS Backdoors
IIS Extensions As Backdoors Microsoft recently published an interesting blog explaining how they’ve noticed a new trend where attackers have been leveraging Internet Information Services (IIS) extensions to covertly backdoor Windows servers: https://www.microsoft.com/security/blog/2022/07/26/malicious-iis-extensions-quietly-open-persistent-backdoors-into-servers/ The Microsoft post contains a wealth of information on this topic, but I really wanted to dig through the specifics in order…
Written by

-
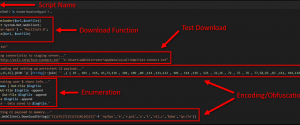
Defending Against PowerShell Attacks
It’s no secret that I am a big fan of PowerShell and recently I have been spending a considerable amount of time researching and testing it from a security perspective. While there is a lot of solid information out there, I have found it can still be a challenge to really get a solid grasp…
Written by
-
Gathering Windows, PowerShell and Sysmon Events with Winlogbeat – ELK 7 – Windows Server 2016 (Part II)
In part I of this series, Installing ELK 7 (Elasticsearch, Logstash and Kibana) on Windows Server 2016, I covered the following: Installing and configuring Elasticsearch, Logstash, and Kibana as Windows services Installing and configuring Winlogbeat to forward logs from the ELK server into ELK Installing and configuring Curator as a scheduled task (optional) Now, in…
Written by

-
Installing ELK 7 (Elasticsearch, Logstash and Kibana) – Windows Server 2016 (Part I)
I am a huge fan of the Elastic stack as it can provide a great deal of visibility into even the largest of environments, which can help enable both engineering and security teams rapidly triage technical issues or incidents at scale. There’s also the fact that unlike Splunk, the Elastic software is free to use…
Written by

-
ELK Stack – Installing and Configuring Curator
In this post I am going to quickly cover what is needed to get Curator up and running on the ELK stack. In the last few posts about the ELK stack I covered everything needed to get it installed, configured and ingesting logs reliably. If you missed those posts, you can find them here: ELK…
Written by

-
ELK Stack – Tips, Tricks and Troubleshooting
This post is going to be a sort of a follow up to my ELK 5 on Ubuntu 16.04 series. I am going to cover some of the lessons I have learned over the last few months of maintaining a running ELK stack instance. I am also going to cover some one liners that can…
Written by

-
ELK 5: Setting up a Grok filter for IIS Logs
In Pt. 3 of my setting up ELK 5 on Ubuntu 16.04 series, I showed how easy it was to ship IIS logs from a Windows Server 2012 R2 using Filebeat. One thing you may have noticed with that configuration is that the logs aren’t parsed out by Logstash, each line from the IIS log…
Written by

-
ELK 5 on Ubuntu 16.04
In this series of posts I am going to cover everything needed to get Elasticsearch, Logstash and Kibana (ELK) up and running on Ubuntu 16.04. In the videos I use the desktop version of Ubuntu, but the process should be the same on the server version. In addition to the ELK stack I will also…
Written by

-
ELK 5 on Ubuntu: Pt. 3 – Installing and Configuring Beats Agents on Windows Clients
In the previous two posts I went over everything from installing Ubuntu to getting the ELK stack setup and ingesting logs from itself. Now in this final post in the series I am going to cover collecting Windows Event and IIS logs from remote Windows clients. Here is the quick run down of exactly what…
Written by

-
ELK 5 on Ubuntu: Pt. 2 – Installing and Configuring Elasticsearch, Logstash, Kibana & Nginx
In part one of this series, I went over the basics of installing and configuring Ubuntu 16.04. Now in this part, I am going to take that same VM and go over everything needed to create a functional ELK stack on a single server. By the end of this post the ELK stack will be…
Written by
