Tag: security
-
Building A Purple Team Lab – Module 3: Atomic Red Team
Intro Additional Modules Building A Purple Team Lab – Module 1: Lab Overview & Outline Building A Purple Team Lab – Module 2: EDR Deployment Building A Purple Team Lab – Module 3: Atomic Red Team Atomic Red Team Atomic Red Team is an open-source project featuring a library of atomic tests combined with a…
Written by

-
Building A Purple Team Lab – Module 2: EDR Deployment
Intro Additional Modules Building A Purple Team Lab – Module 1: Lab Overview & Outline Building A Purple Team Lab – Module 2: EDR Deployment Building A Purple Team Lab – Module 3: Atomic Red Team The Elastic Container Project The Elastic Container Project will serve as our Endpoint Detection & Response (EDR) solution for…
Written by

-
Building A Purple Team Lab – Module 1: Lab Overview & Outline
Overview This will be a multi-part series focused on setting up a Purple Team lab with the following high-level goals in mind: Locally hosted using open-source software where possible (Free) Deploy & configure an Endpoint Detection & Response (EDR) solution Gain hands on experience testing basic red team tactics, techniques, and procedures (TTPs) on Windows…
Written by

-
Analyzing & Detecting IIS Backdoors
IIS Extensions As Backdoors Microsoft recently published an interesting blog explaining how they’ve noticed a new trend where attackers have been leveraging Internet Information Services (IIS) extensions to covertly backdoor Windows servers: https://www.microsoft.com/security/blog/2022/07/26/malicious-iis-extensions-quietly-open-persistent-backdoors-into-servers/ The Microsoft post contains a wealth of information on this topic, but I really wanted to dig through the specifics in order…
Written by

-
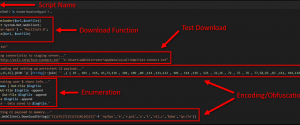
Defending Against PowerShell Attacks
It’s no secret that I am a big fan of PowerShell and recently I have been spending a considerable amount of time researching and testing it from a security perspective. While there is a lot of solid information out there, I have found it can still be a challenge to really get a solid grasp…
Written by
-
Gathering Windows, PowerShell and Sysmon Events with Winlogbeat – ELK 7 – Windows Server 2016 (Part II)
In part I of this series, Installing ELK 7 (Elasticsearch, Logstash and Kibana) on Windows Server 2016, I covered the following: Installing and configuring Elasticsearch, Logstash, and Kibana as Windows services Installing and configuring Winlogbeat to forward logs from the ELK server into ELK Installing and configuring Curator as a scheduled task (optional) Now, in…
Written by

-
Installing ELK 7 (Elasticsearch, Logstash and Kibana) – Windows Server 2016 (Part I)
I am a huge fan of the Elastic stack as it can provide a great deal of visibility into even the largest of environments, which can help enable both engineering and security teams rapidly triage technical issues or incidents at scale. There’s also the fact that unlike Splunk, the Elastic software is free to use…
Written by

-
Home Lab Cooling Upgrade!
In this video I show off my latest project – Upgrading the cooling system on my home lab in hopes of making it a little more efficient while quieting things down a bit. The original setup consisted of the following: 2 x 6″ Ducts with Fans 6″ Flexible Ducting Originally there was just a single…
Written by

-
My Journey Into The OSCP
Intro This post is going to break away from my typical technical how-to style posts, and talk a little bit about something that has been a personal goal of mine for some time – The Offensive Security Certified Professional. When it comes to even thinking about enrolling in the OSCP, most people will question if…
Written by

-
Home Lab Setup (2017)
In this post and video I give a quick run down of my Home Lab – everything from the rack itself, to the hardware and the basics of what everything is being used for. I started this project towards the end of 2012 with a single Dell PowerEdge 2950 GII and was hoping to teach…
Written by
