Category: Computers
-
Building A Purple Team Lab – Module 3: Atomic Red Team
Intro Additional Modules Building A Purple Team Lab – Module 1: Lab Overview & Outline Building A Purple Team Lab – Module 2: EDR Deployment Building A Purple Team Lab – Module 3: Atomic Red Team Atomic Red Team Atomic Red Team is an open-source project featuring a library of atomic tests combined with a…
Written by

-
Building A Purple Team Lab – Module 2: EDR Deployment
Intro Additional Modules Building A Purple Team Lab – Module 1: Lab Overview & Outline Building A Purple Team Lab – Module 2: EDR Deployment Building A Purple Team Lab – Module 3: Atomic Red Team The Elastic Container Project The Elastic Container Project will serve as our Endpoint Detection & Response (EDR) solution for…
Written by

-
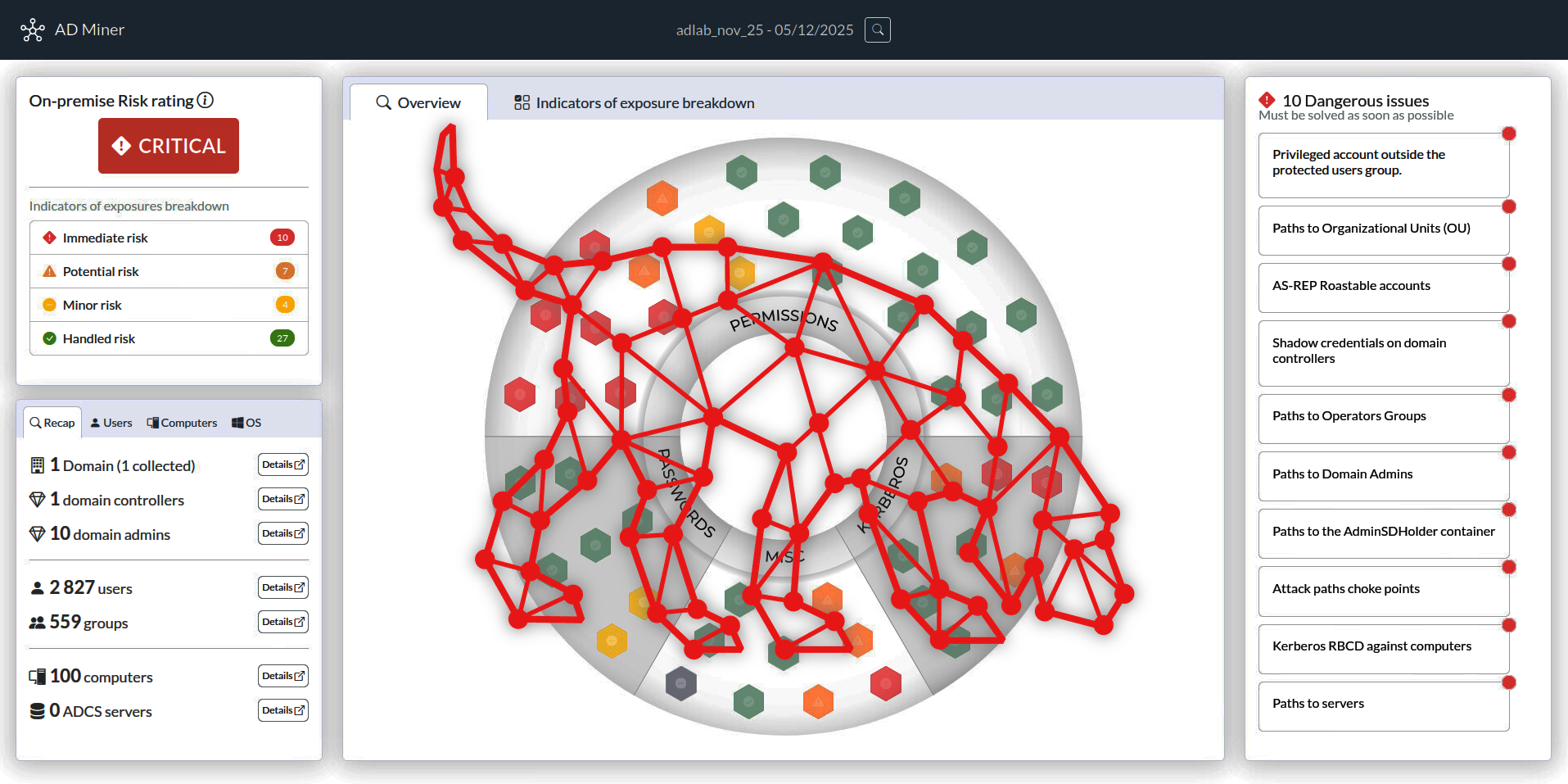
Building A Purple Team Lab – Module 1: Lab Overview & Outline
Overview This will be a multi-part series focused on setting up a Purple Team lab with the following high-level goals in mind: Locally hosted using open-source software where possible (Free) Deploy & configure an Endpoint Detection & Response (EDR) solution Gain hands on experience testing basic red team tactics, techniques, and procedures (TTPs) on Windows…
Written by

-
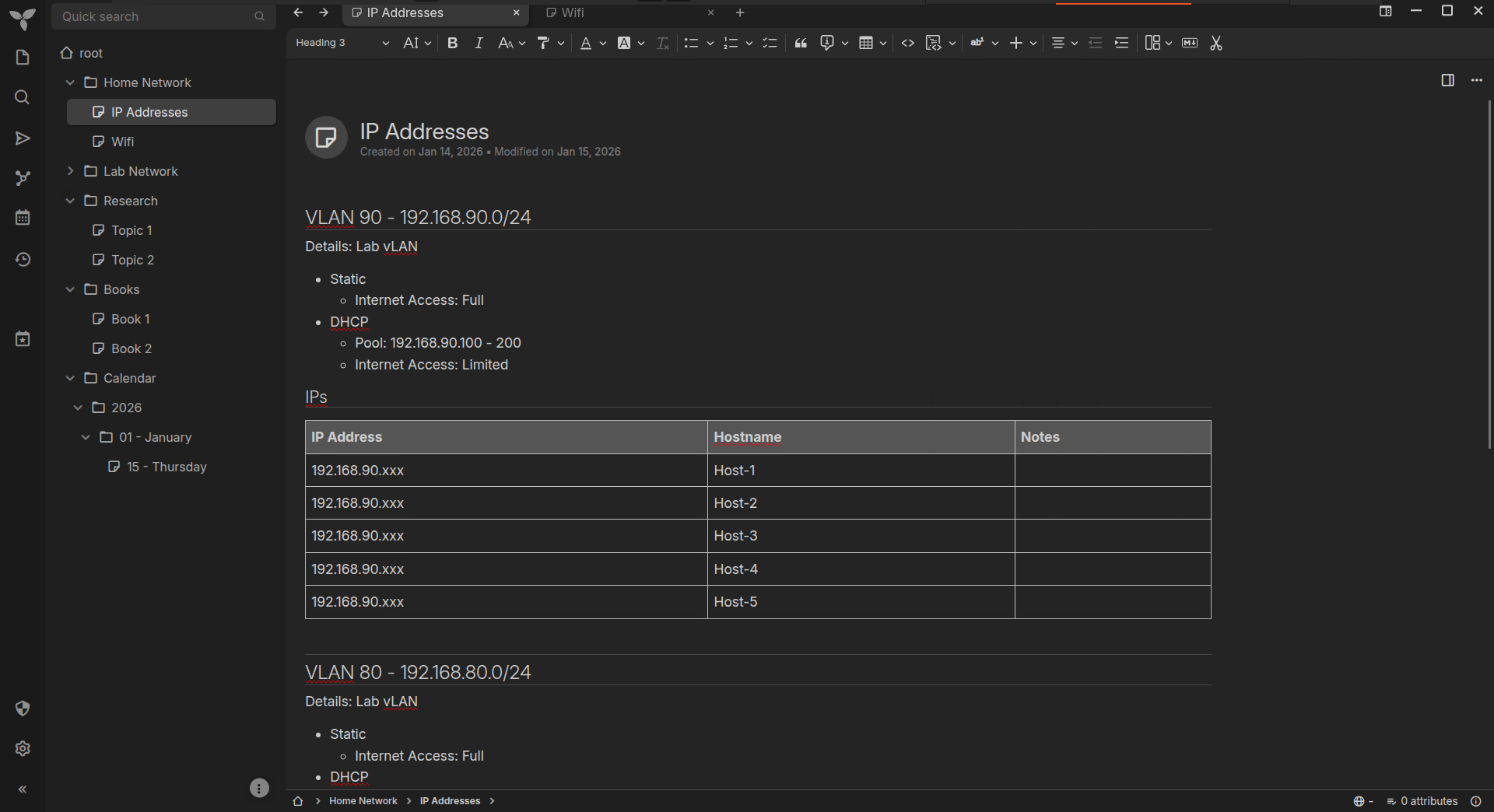
Trilium Notes – Self-Hosted Server Setup
I’ve been looking for a OneNote alternative for a few years now, but haven’t been able to find anything that combines the same basic functionality with a simple, clean interface. As I’m increasingly moving away from Microsoft products, I realized it was time to find a dedicated solution and stick with it. I’m excited to…
Written by
-
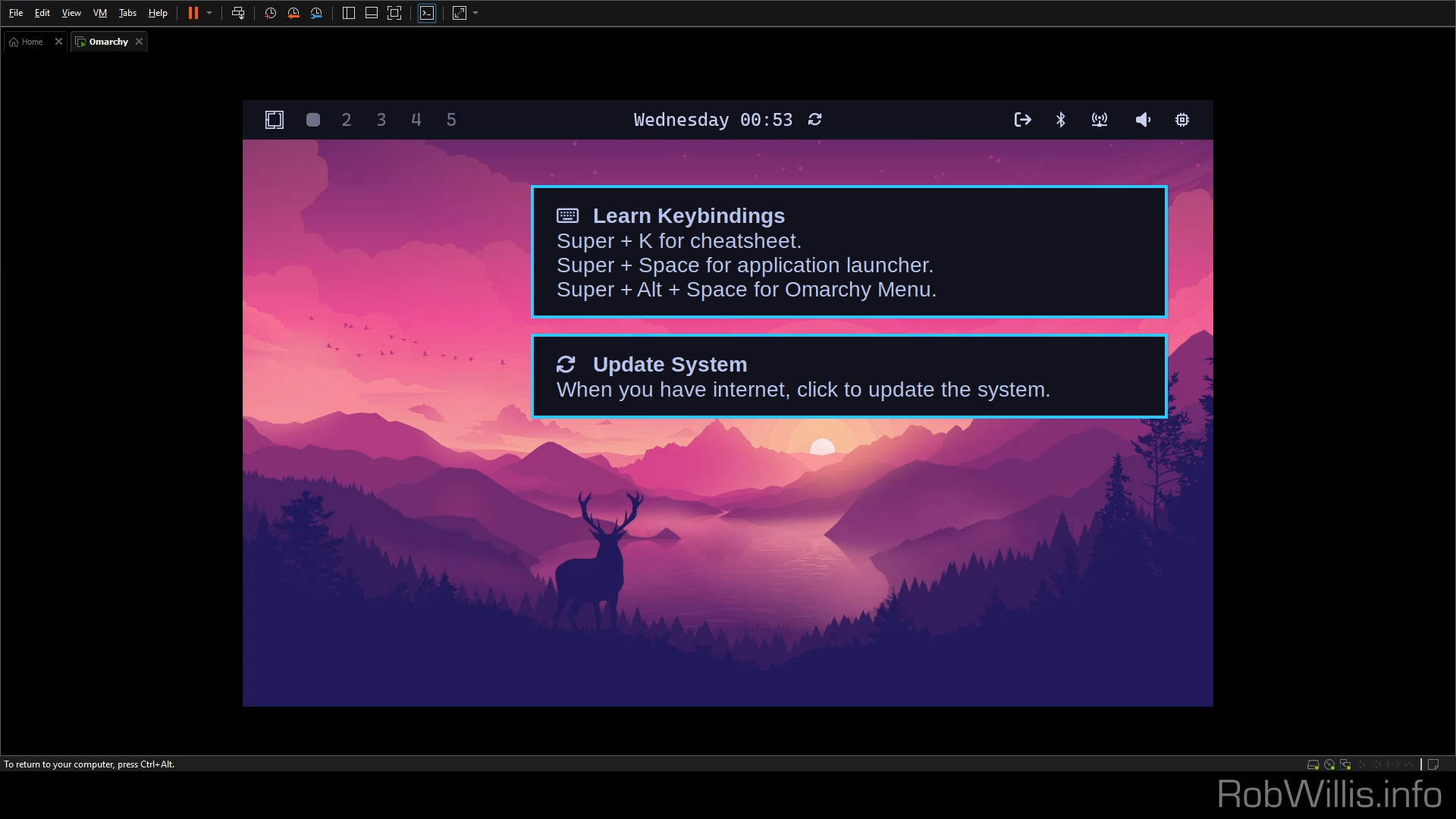
Installing Omarchy On VMware Workstation
Update – February 23, 2026 After some great feedback from the YouTube community, here’s a list of additional tips and troubleshooting steps for those still experiencing issues: VMware Workstation Specific Ensure Open VM Tools is installed and running Keep the VM in full screen mode and the mouse focused Set the resolution lower than the…
Written by
-
Home Lab (2025)
It’s been a while since I’ve made a video, and even longer since I’ve shown my home lab setup! I’ve been doing some cleaning and thinking about upgrades, so I figured now would be a good time to show where everything currently stands.
Written by

-
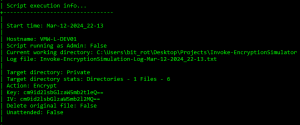
Introducing Invoke-EncryptionSimulator: A PowerShell Tool for Simulating Late-Stage Ransomware Attacks
Invoke-EncryptionSimulator Invoke-EncryptionSimulator is designed to be a simple and safe way to emulate the encryption stage of a ransomware deployment to aid in development and testing of controls focusing on file system level changes rather than process related telemetry. Invoke-EncryptionSimulator is designed to be a simple and safe way to emulate the encryption stage of…
Written by
-
Analyzing & Detecting IIS Backdoors
IIS Extensions As Backdoors Microsoft recently published an interesting blog explaining how they’ve noticed a new trend where attackers have been leveraging Internet Information Services (IIS) extensions to covertly backdoor Windows servers: https://www.microsoft.com/security/blog/2022/07/26/malicious-iis-extensions-quietly-open-persistent-backdoors-into-servers/ The Microsoft post contains a wealth of information on this topic, but I really wanted to dig through the specifics in order…
Written by

-
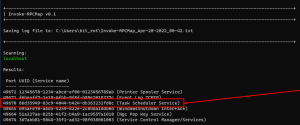
New Tool! Invoke-RPCMap: PowerShell Script for Remote RPC Service Enumeration
Invoke-RPCMap Invoke-RPCMap can be used to enumerate local and remote RPC services/ports via the RPC Endpoint Mapper service. This information can useful during an investigation where a connection to a remote port is known, but the service is running under a generic process like svchost.exe. This script will do the following: Create a local log…
Written by